Cluster Connect#
Lens premium subscription feature. See details on Lens Pricing.
Secure Access Sharing to Kubernetes Clusters#
Sharing access to Kubernetes clusters can be challenging. You might have to work with IAMs from different providers, have a bunch of dedicated tooling installed, get access to kubectl files, make those files work with your kubectl and finally ensure you are in the same network with the target cluster API. Because of this difficulty, users might bypass security best practices. We have addressed this challenge and made it easy for Lens users to access and share access to clusters without compromising security.
When you use Spaces, you’ll get the option to share access to your cluster and accept invitations from others to access their clusters. To make this possible, we created Cluster Connect. It allows Lens users to connect any of their clusters to Spaces without requiring an inbound port to be enabled on the firewall. It utilizes end-to-end encryption to secure connections between users and clusters, eliminating the need for a VPN. This means there is no need to expose the Kubernetes API via the Internet. Developers and operators can access and work with their Kubernetes clusters easily from anywhere.
Cluster Connect Technical Details#
- Cluster Connect is based on BoreD OSS software:
- A BoreD Service(OSS container image) per Space is used to create a secure tunnel between Lens Desktop and the cluster
- A BoreD Agent is a one-time install on the shared cluster and uses the native Kubernetes impersonate functionality (industry standard)
- A BoreD Client embedded in Lens Desktop and based on bored-mplex
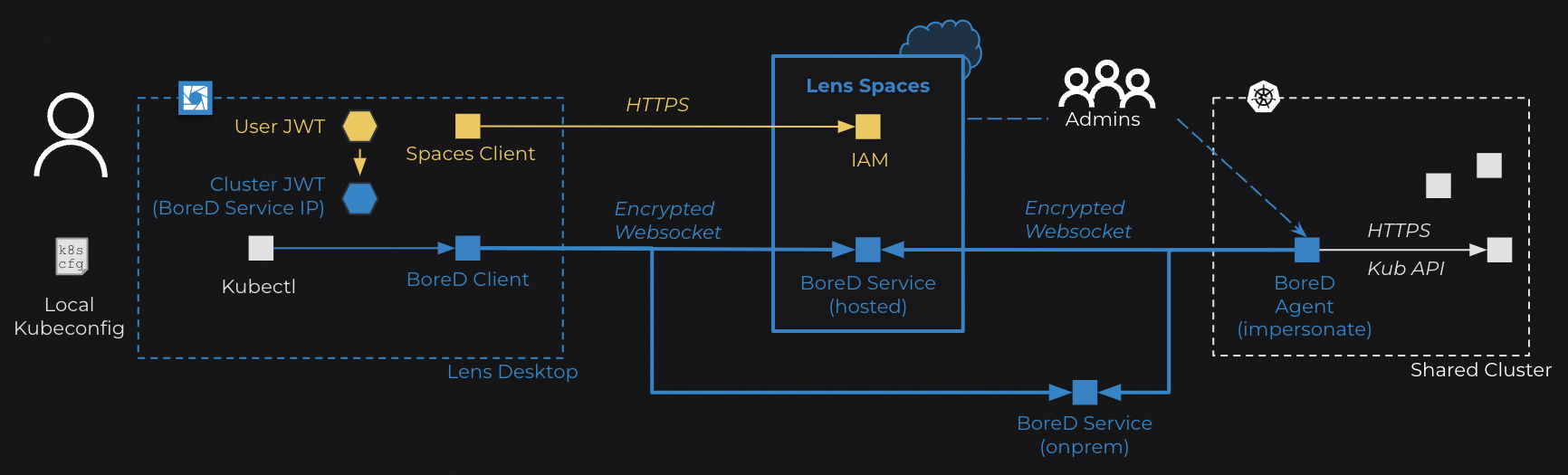
- When you share a cluster you will be prompted to install a BoreD Agent in the shared cluster. You must have the required permissions to install the agent.
- The BoreD Agent will open an authenticated and secure connection from the cluster to Lens Spaces using Secure WebSockets(TLS).
- When a user wants to access the shared cluster they first authenticate with Lens Spaces and a User JWT is issued.
- If the user has authorization to access the shared cluster, Lens Desktop will generate a locally stored kubeconfig file with instructions on how to obtain a Cluster JWT based on the user's identity. Lens Spaces does not store this generated kubeconfig file.
- When a user wishes to connect to the shared cluster a Cluster JWT is generated containing a BoreD Service address. The generated local kubeconfig references the generated Cluster JWT for access to the shared cluster. The Cluster JWT is reissued every 24 hours.
- The generated local kubeconfig file is used by the embedded BoreD Client to tunnel requests to the shared cluster via the BoreD Service
- The BoreD Service does not store any data, it only proxies and relays encrypted data from Lens Desktop to the shared cluster.
- The BoreD Agent translates requests to match desired Kubernetes RBAC user / group.
Transport Layer Encryption#
Both client and agent use web sockets to establish a socket connection to BoreD daemon. This transport layer is secured using Secure WebSockets (TLS).
Tunnel Encryption#
BoreD tunnel encryption is done in two phases. Tunneled data is encrypted using symmetric encryption (AES-256-GCM). Key exchange is done using asymmetric encryption (RSA-4096) where the BoreD agent has the private key and the public key is distributed to clients via the BoreD daemon.
Cluster Connect Regions#
Cluster Connect supports different Regions for the Lens K8S Proxy Server infrastructure. Choose a region which is geographically closest to the cluster when installing the Cluster Connect agent to maximize performance.
Supported Regions:
- Europe
- United States of America
In order to change the region you need to uninstall and re-install the Cluster Connect Agent in the Cluster Settings menu of your cluster.
Cluster Connect IP Allowlist#
In order for Teamwork Cluster Connect to function correctly the following IP addresses must be reachable by the Kubernetes cluster.
We recommend monitoring the page, as this list may be changed periodically.
Europe Region#
- 54.170.30.95
- 54.154.43.89
United States of America Region#
- 3.142.108.50
- 3.23.198.115
In order for a space to function correctly the following IP addresses must be reachable by Lens Desktop:
IPv4 List#
- 199.83.128.1 - 199.83.135.254
- 198.143.32.1 - 198.143.63.254
- 149.126.72.1 - 149.126.79.254
- 103.28.248.1 - 103.28.251.254
- 185.11.124.1 - 185.11.127.254
- 45.64.64.0 - 45.64.67.255
- 192.230.64.1 - 192.230.127.254
- 107.154.0.0 - 107.154.255.254
- 45.60.0.1 - 45.60.255.254
- 45.223.0.1 - 45.223.255.254
- 131.125.128.1-131.125.255.254
IPv6 List#
- 2a02:e980:0:0:0:0:0:0 - 2a02:e987:ffff:ffff:ffff:ffff:ffff:ffff